Greenplum is a powerful database management system used by many organizations to handle large volumes of data. As companies store more sensitive information, protecting this data becomes crucial. Dynamic data masking in Greenplum protects sensitive information while letting authorized users access it. This article explores the concept of dynamic data masking in Greenplum, its benefits, and how to implement it effectively.
What does Dynamic Data Masking mean?
Dynamic data masking is a security measure that conceals confidential information instantly. It works by replacing original values with masked versions when unauthorized users query the database. The actual data remains unchanged in the database, but users without proper permissions see only the masked information. This approach differs from static data masking, which permanently alters the data.
Greenplum dynamic data masking provides several advantages for organizations. It enhances security by protecting sensitive information from unauthorized access, reducing the risk of data breaches. It helps meet regulatory requirements like GDPR, HIPAA, and CCPA.
Administrators can easily adjust masking rules without modifying the underlying data. It doesn’t require changes to existing applications or database structures. Dynamic masking has minimal impact on query performance.
Greenplum dynamic data masking operates at the query level. When a user sends a query, the database engine checks their permissions. If the user lacks the necessary rights, the engine applies masking rules to sensitive columns before returning the results. This process happens transparently, without the user’s knowledge.
Implementing Dynamic Data Masking in Greenplum
To set up dynamic data masking in Greenplum, follow these steps:
First, identify the columns containing sensitive information. Common examples include Social Security numbers, credit card numbers, email addresses, phone numbers, and addresses.
Next, create custom functions to mask different types of data. Here’s an example of a function to mask email addresses:
CREATE OR REPLACE FUNCTION mask_email(email text) RETURNS text AS $$ BEGIN RETURN LEFT(email, 1) || '***@' || SPLIT_PART(email, '@', 2); END; $$ LANGUAGE plpgsql;
This function keeps the first character of the email, replaces the rest with asterisks, and preserves the domain.
After creating masking functions, apply them to the relevant columns. Use views or security policies to implement the masking:
CREATE VIEW masked_customers AS SELECT id, name, mask_email(email) AS email, mask_phone(phone) AS phone FROM customers;
Grant appropriate permissions to users and roles. Ensure that only authorized users can access the original data:
GRANT SELECT ON masked_customers TO analyst_role; GRANT SELECT ON customers TO admin_role;
Finally, test the masking implementation to ensure it works as expected:
-- As an analyst SELECT * FROM masked_customers LIMIT 5; -- As an admin SELECT * FROM customers LIMIT 5;
Verify that analysts see masked data while admins can view the original information.
Implementation via DataSunrise
Greenplum offers dynamic masking, but some users find it too complex for large databases. In these cases, experts advise using third-party solutions. To perform this in DataSunrise, you must take several steps.
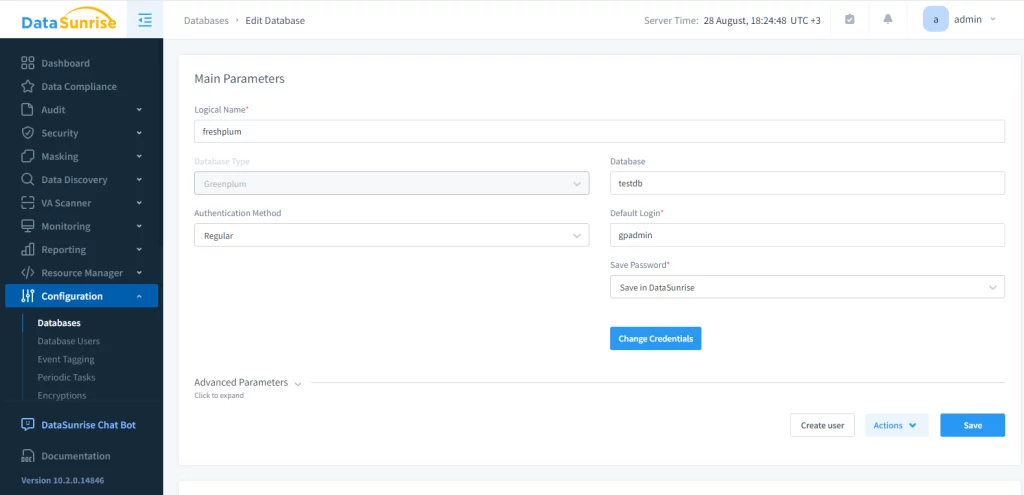
Firstly, you need to create an instance of the target database. Through the instance a user is able to interact with the target database via security rules and masking tasks. Creating an instance:
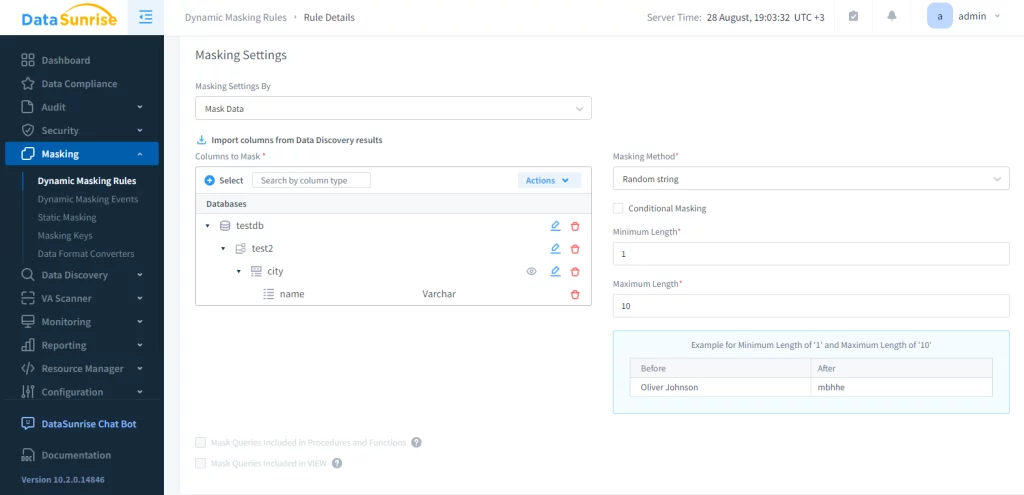
All that’s left is to create a masking rule and turn it on. Select the database, schema, table and columns and the methods of masking. In this example we’ll mask the ‘city’ table of ‘test2’ database.
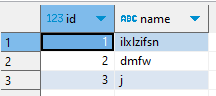
The result is as follows:
Best Practices and Challenges
To maximize the effectiveness of dynamic data masking in Greenplum, consider these best practices:
Apply consistent masking rules across all instances of sensitive data. This approach maintains data integrity and prevents confusion.
Conduct regular audits of your masking policies. Ensure they align with current security requirements and regulations.
Monitor the performance impact of dynamic masking. Optimize masking functions and policies if needed to minimize query overhead.
Educate users about dynamic data masking. Help them understand why they might see masked data and how to request access if necessary.
Although Greenplum’s dynamic data masking provides substantial advantages, it’s crucial to recognize possible obstacles. Masking can complicate certain types of queries, especially those involving complex joins or aggregations. Maintaining data relationships across masked and unmasked tables requires careful planning.
Dynamic masking shouldn’t be the only security measure. It works best as part of a comprehensive data protection strategy.
Future of Dynamic Data Masking in Greenplum
As data privacy concerns grow, we can expect further advancements in Greenplum dynamic data masking. Future versions may offer even more efficient masking techniques.
We might see more sophisticated masking options, such as format-preserving encryption. Better integration with other Greenplum security features and third-party tools is likely. Tools to automatically adjust masking rules based on changing regulations may emerge.
Conclusion
Dynamic data masking in Greenplum provides a powerful way to protect sensitive information without sacrificing database functionality. By implementing this feature, organizations can enhance their data security, comply with regulations, and maintain user trust. As you explore Greenplum dynamic data masking, remember that it’s just one part of a comprehensive data protection strategy. Combine it with other security measures to create a robust defense against data breaches and unauthorized access.